Thick client
Penetration Testing
Secure Your Thick Client,
Protect Your Data Where It Lives.
Thick Client Penetration Tests identifies unique and critical vulnerabilities found in applications that run locally on a user’s machine. Unlike web applications that primarily process data on a server, thick clients perform a significant amount of processing and data storage on the client side, creating a larger and more complex attack surface. We perform our tests based on industry recognised standards, OWASP Top 10 Desktop Application Security Risks which covers the following risks:
Input Injections
Broken Authentication & Session Management
Sensitive Data Exposure
Improper Cryptography Usage
Improper Authorisation
Security Misconfiguration
Insecure Communication
Poor Code Quality
Using Components with Known Vulnerabilities
Insufficient Logging & Monitoring
Secure Your Thick Client,
Protect Your Data Where It Lives.
Thick Client Penetration Tests identifies unique and critical vulnerabilities found in applications that run locally on a user’s machine. Unlike web applications that primarily process data on a server, thick clients perform a significant amount of processing and data storage on the client side, creating a larger and more complex attack surface. We perform our tests based on industry recognised standards, OWASP Top 10 Desktop Application Security Risks which covers the following risks:
Input Injections
Broken Authentication & Session Management
Sensitive Data Exposure
Improper Cryptography Usage
Improper Authorisation
Security Misconfiguration
Insecure Communication
Poor Code Quality
Using Components with Known Vulnerabilities
Insufficient Logging & Monitoring
Hardening Your Thick Client Applications Using Proven Security Frameworks
We perform thick-client application penetration testing based on industry recognised standards, OWASP Top 10 Desktop Application Security Risks.
Our testing uses a combination of tools, techniques, and custom approaches to determine whether it is possible for an attacker to:
Bypass Authentication
Circumvent authentication and authorisation mechanisms.
Privilege Escalation
Perform vertical or horizontal privilege escalation.
Access Control Exploitation
Bypass access controls or application restrictions.
Unauthorized Data Access
Access or modify unauthorised data.
Cryptographic Weaknesses Exploitation
Break or analyse cryptography used within user accessible components.
Actionable Recommendations You Can Bring To Stakeholders
We deliver comprehensive, cryptographically signed penetration testing reports that are both verifiable and tamper-proof. Each report includes detailed vulnerability backgrounds, clear impact assessments, and actionable recommendations. And because security is a global concern, our reports are available in 113 languages—ensuring your cross-border teams are always in the know.
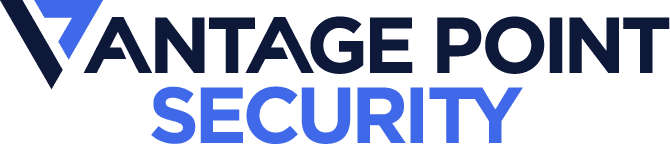
Compliance Verification Reporting
The report clearly shows the specific standards the app complies to.
Detailed down to the Test Cases
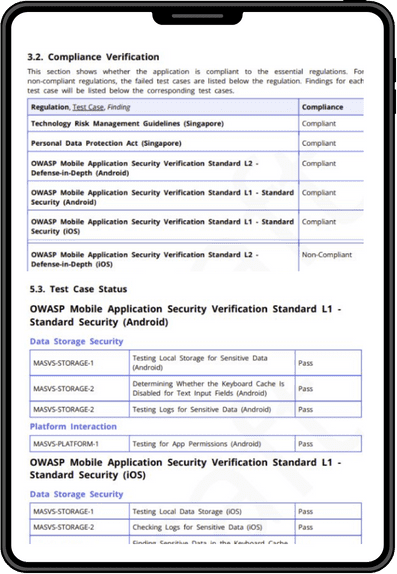
Detailed Background
We explain the vulnerability clear enough for technical and non technical stakeholders to understand.
Impact statements
Explaining the business impact of the vulnerability.
Recommendations
Actionable insights stakeholders can take to remediate gaps.
SPEAK TO AN EXPERT
Know Your Vulnerabilities.
Start Securing your Assets Today.
Experts in Penetration Testing
innovation and IP development
Red Team Providers in Southeast Asia
80,000+ hours of yearly pentesting
Specialists in AppSec
Quality Assurance with Velocity
Other CREST Approved Penetration Testing Services
Web Application
We secure your web applications by identifying injection flaws, authentication bypasses, and business logic vulnerabilities that could expose your systems, ensuring compliance to technical and regulatory standards.
Mobile Application
We secure your iOS and Android applications by identifying code vulnerabilities, insecure data storage, and authentication flaws, ensuring compliance to standards like the OWASP MASVS and more.
Wireless Network
We secure your Wi-Fi and wireless communication systems through targeted testing that identifies encryption flaws, authentication weaknesses, and connection protocol vulnerabilities.
API
We secure your APIs against data breaches and unauthorized access by identifying authentication flaws, injection vulnerabilities, and more in your API endpoints, ensuring compliance to standards like OWASP Top 10 and more.
Thick Client
We secure your desktop applications through thorough testing that identifies local storage vulnerabilities, communication protocol weaknesses, and authentication flaws that could compromise user data.
Active Directory
We secure your Active Directory infrastructure through specialized testing that identifies privilege escalation paths, credential vulnerabilities, and configuration weaknesses that could lead to domain compromise.
Other CREST Approved Penetration Testing Services
Mobile Application
We secure your iOS and Android applications by identifying code vulnerabilities, insecure data storage, and authentication flaws, ensuring compliance to standards like the OWASP MASVS and more.
Web Application
We secure your web applications by identifying injection flaws, authentication bypasses, and business logic vulnerabilities that could expose your systems, ensuring compliance to technical and regulatory standards.
Network
We secure your network infrastructure by identifying misconfigurations, weak protocols, and access control flaws across routers, switches, servers, and endpoints. We ensure compliance to many industry standards.
Wireless Network
We secure your Wi-Fi and wireless communication systems through targeted testing that identifies encryption flaws, authentication weaknesses, and connection protocol vulnerabilities.
API
We secure your APIs against data breaches and unauthorized access by identifying authentication flaws, injection vulnerabilities, and more in your API endpoints, ensuring compliance to standards like OWASP Top 10 and more.
Active Directory
We secure your Active Directory infrastructure through specialized testing that identifies privilege escalation paths, credential vulnerabilities, and configuration weaknesses that could lead to domain compromise.